This week was bananas…but not in a bad way. I went to LinkedIn to settle a debate with my wife on the optimal ripeness of bananas based on the guide below.

The results were all over the place, but the general consensus was mostly yellow, which is the only correct answer. The outlier was Bailey Marshall, a self-proclaimed monster who opted for a 2-3. We forgave her because she’s awesome and worth a follow on LinkedIn.
Anywho, today in the cyber and AI world, we’re covering:
AI is tearing companies apart
A new way to bypass MFA
ChatGPT is throwing shade at a Norwegian dude
-Jason
p.s. it’s not every day that you see a spaceship blow up while flying in a commercial airplane.
AI Spotlight
AI is tearing companies apart!

A growing divide between executives and employees isn’t about remote work. It’s also about the use of AI. New survey results from Writer shed light on the situation.
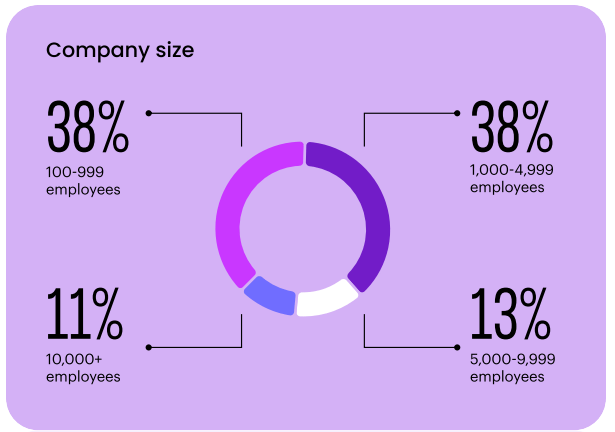
The survey covered 1,600 people. This included 800 C-suite executives and 800 employees in finance, HR, legal, marketing, sales, and customer service who are actively using AI. Notably missing are tech teams, which I’d be very interested to understand how they impact the results. Either way, let’s dig in.
Let’s start with where executives and employees agree. Both groups said GenAI largely benefited them. The largest benefit was having more time to “focus on strategy,” which could be another way of saying “scrolling on their phones.”
The ability to make better and faster data-driven decisions was a close second for the C-suite, which also could be another way of finding a scapegoat when a decision didn’t pan out. Just blame it on AI.
Let’s move to the challenges that are tearing companies apart. Many of them concern things that make us human (+1 points for robots): miscommunication, power struggles, and fear.
Miscommunication: In the most unsurprising finding, the C-suite and employees see reality differently. While the execs feel things are going smoothly and everyone is on the same page, the employees’ perceptions are very different. This is something I’ve witnessed in most companies on any company strategy.
This tells me that execs must listen more to employees and continuously communicate the company’s AI strategy every chance they can.
Power Struggles: 71% of the C-suite said that GenAI applications are being created in a silo, with 68% saying the adoption has created tension or division between IT teams and the rest of the business.
This has resulted in 49% of employees feeling as though they have been left to figure out GenAI on their own. No wonder why silos are being created. Those silos lead each group to build their own solution, which makes them think their way is the best way, which leads to infighting. I think this is tied to the miscommunication I mentioned above.
Further evidence in the survey supports this. The writer stated that the businesses most successful in deploying AI are those where “IT is collaborating across the business to drive value.” A clear strategy that drives collaboration with a core enabler (IT) is very powerful.
Fear: What stood out most to me was that 41% of Millenial and GenZ employees admit to “sabotaging their company’s AI strategy” out of fear of losing their creativity, losing their jobs, and the low-quality AI tools their company offers.
It is very interesting to me that companies are now asking their employees to adopt the technology they are saying will replace many employees in the future. This could leave people thinking they’re digging their own grave.
I believe AI will enable employees to go faster and further with less effort. So, it’s more of a shift toward employee enablement rather than replacement.
Security Deep Dive
A new way to bypass MFA

I love learning about new attack techniques. This week, my buddy Stu Panensky flagged one I hadn’t heard of. It’s called Browser-in-the-Middle (BiTM). It’s a streamlined Adversary in the Middle (AiTM) attack, which we’ve all come to know, love, and adore for its ability to bypass weaker forms of MFA. If your memory is fuzzy on AiTM, check out my video.
The challenge with AiTM is that it’s complicated to set up. It relies on a transparent proxy, a server that intercepts and forwards network traffic. The proxy sits between the victim and the application they want to log into without configuring anything on the victim’s system. This is good because, like an inside joke, it’s ruined if other people know about it.
Transparent proxies require a lot of customization based on the service you’re trying to impersonate, like Microsoft 365 or Gmail. Some services, like Gmail, are getting better at detecting when this is happening and will block login attempts. Ain’t nobody got time for that. Time to pivot.

A nerdy security researcher proclaimed there’s an easier way! And damn, were they right. Enter stage left, a Browser-in-the-Middle (BiTM) attack.
Here’s how it unfolds:
Step 1: The attacker sets up a server and installs a tool called noVNC. It’s a remote access tool that uses the Virtual Computing Network screen-sharing program. The fun part of this, though, is the “no.” Typically, VNC needs a client installed on another system to access the VNC server, but noVNC runs in your browser.
Step 2: The attacker runs a browser on the server in kiosk mode. Kiosk mode puts the browser into full-screen and hides everything else. It’s exactly what you would expect at any kiosk. If you didn’t realize it, an operating system runs behind most kiosks. You’re just seeing an application running on top of it.
The attacker then preloads a login page on the browser for the service they want to target, such as Gmail or Microsoft 365.
Step 3: The attacker sends the victim a URL to connect to the noVNC server. When the victim clicks on the noVNC link, they connect to the attacker’s server on their browser. The attacker’s server displays the login page for the target application. To the victim, it looks like the webpage loaded in their browser when, in reality, it’s running on the attacker’s server.
The user logs into the application with their valid credentials and, if MFA is enabled (which it better be), will enter their MFA token.
Step 4: The attacker wins. The victim logged into the target application on the attacker’s browser. This is the equivalent of the attacker cleaning up their mom’s basement before guests arrive, the victim flying to the attacker’s house, ringing the doorbell, walking past all of the shoes in the entryway, walking down the creaky wooden stairs into the dank basement, high fiving the attacker, sitting down in the attacker’s gaming chair that looks like a race car seat, wiping the keyboard with a Clorox wipe, and logging into Microsoft 365 on the attacker’s system.
The attacker can access the application as the victim using the browser the victim just used. A nice attacker would offer you snacks before your journey home, but most attackers will log your credentials so they have them for future use.
Oh, and if you’re wondering, naturally, this has all been automated and scripted into a phishing platform. We wouldn’t want to overburden the attackers that much.
But there’s still good news! Our good friend FIDO2 MFA (passkeys) is still working here to stop BiTM. Mandiant has an excellent report on their version of BiTM, which includes all the details and a nice graphic below.

Source: Mandiant BiTM overview

MFA isn’t dead, but it’s not the silver bullet. You need to use phishing-resistant MFA, like passkeys or hardware keys.
Security & AI News
What Else is Happening?
🏷 Starting September 1, 2025, China will require all AI-generated content to have an “explicit identification” to “prevent confusion and misunderstanding” of online content. While labeling AI-generated content is helpful in a country where information is tightly controlled, a similar approach won’t work in other areas. And you can bet that attackers aren’t going to be labeling their deepfakes.
🫵 ChatGPT is throwing shade at a random Norwegian dude. The self-described “regular person” decided to do what everyone does on Google when no one is looking. Search himself. ChatGPT responded, saying that he was currently serving a 21-year prison sentence for murdering his children, which was blatantly false for this regular dude.
💰 Operation Zero, a sketchy Russian platform that pays and resells vulnerabilities to the Russian government, now offers up to $4 million for a Telegram full-chain exploit. A full chain would require multiple exploits in Telegram and the underlying operating system to gain full privileges over the device. According to the Operation Zero website, exploits targeting mobile devices are much more lucrative, often due to their increased difficulty.
😲 This went from bad to really creepy. This week, a former Michigan assistant football coach was charged for hacking into student-athlete databases at over 100 colleges. Per the complaint, what started as compromising account passwords for the databases turned into downloading PII and PHI for over 150K athletes and then targeting female athletes’ information to gain access to their social media, email, and cloud storage accounts for over 2,000 athletes! With that access, he searched for and downloaded “personal, intimate photographs and videos that were not publicly shared.”
🤖 North Korea is launching a new hacking unit called Research Center 227. This unit will develop “offensive hacking technologies and programs.” Specifically, it will use AI to improve its techniques for stealing crypto. The unit will start with 90 “computer experts” sourced from universities. This comes after North Korea stole $1.5 billion from Bybit, so I can’t wait to see what happens next.
If you enjoyed this, forward it to a fellow cyber nerd.
If you’re that fellow cyber nerd, subscribe here.
See you next week, nerd!