I just want to go on record as saying that you can have too much cheese on a grilled cheese sandwich. Let’s set some ground rules.
If the sandwich weighs more than a brick, you’ve gone too far.
If you’re melting cheese outside the sandwich, you’ve gone too far.
And, if your grilled sandwich tastes like a Cheez-It, you’ve gone too far.
I’m not bitter…anyway, today in the cyber world we’re covering:
A spooky new AI tool for hackers
Follow me through an EZPass text scam (I had too much fun with this)
Remember HP?
-Jason
p.s. I hope you can find as much joy in something as much as this dude does.
AI Spotlight
A Spooky New AI Tool for Hackers

Security researchers at Abnormal Security published research on a new ChatGPT-esque tool for cybercriminals. Known as GhostGPT, it operates as a wrapper for ChatGPT. It works by jailbreaking ChatGPT to remove all of ChatGPT’s protective functions, like not returning instructions on hacking or doing other nefarious things that ChatGPT would typically stop.

The obvious use for tools like this is to automate much of the social engineering tasks involved in hacking. Abnormal’s team tested creating a phishing email from DocuSign…it was pretty good.

If you were to try to do this in ChatGPT, it would just outright refuse to give you an answer. Now, crafty prompters could go generic enough in ChatGPT to avoid tripping those alarms, but why bother when GhostGPT does the heavy evasion lifting for you?
This isn’t the first cybercrime-focused GPT to pop up, nor will it be the last. While the other ones felt a bit more scammy, this one has some real vibes to it. We’ll see how long it sticks around. The biggest limiting factor for it will be when ChatGPT catches on and fixes whatever jail-breaking methods GhostGPT uses.
Security Deep Dive
Jump Into an EZPass Text Scam

I don’t want to start a debate about how Android phones are better than iPhones (because they are). However, I’ve found that Android phones typically do a better job of filtering out spam text messages—something I always like to point out to my many iPhone friend users.
This week, I noticed a new tactic bypassing the filters. One of the texts that got through was the classic EZPass scam. Since it hit my radar, I decided to follow the scam right to the end. Let’s dig in.
The scam starts with a group message. The scammers start a group thread with less than ten people and immediately remove me. I will try not to take any offense to not being left in the group, but it’s been hard.
The text states that my vehicle has an unpaid toll and provides a link to pay it. How helpful! As a good citizen, I obviously had to follow the link.

I wouldn’t do this from my phone, so I went to my virtual lab and visited the link. However, it just directed me to a Google query page that said “blocked.” This is not cool, but it's also not the end of the story. We won’t be defeated that easily.
Given the link came in a text message. I figured the scammers only wanted you to visit from your mobile device and were filtering out anyone else. Every web request you make includes a User Agent string. It just says what type of browser and device you’re using. And because it comes from you, you can also change it.
So, I just changed the User Agent string in my browser to say it was Chrome on an Android device. Voila, I was able to visit the scam page.

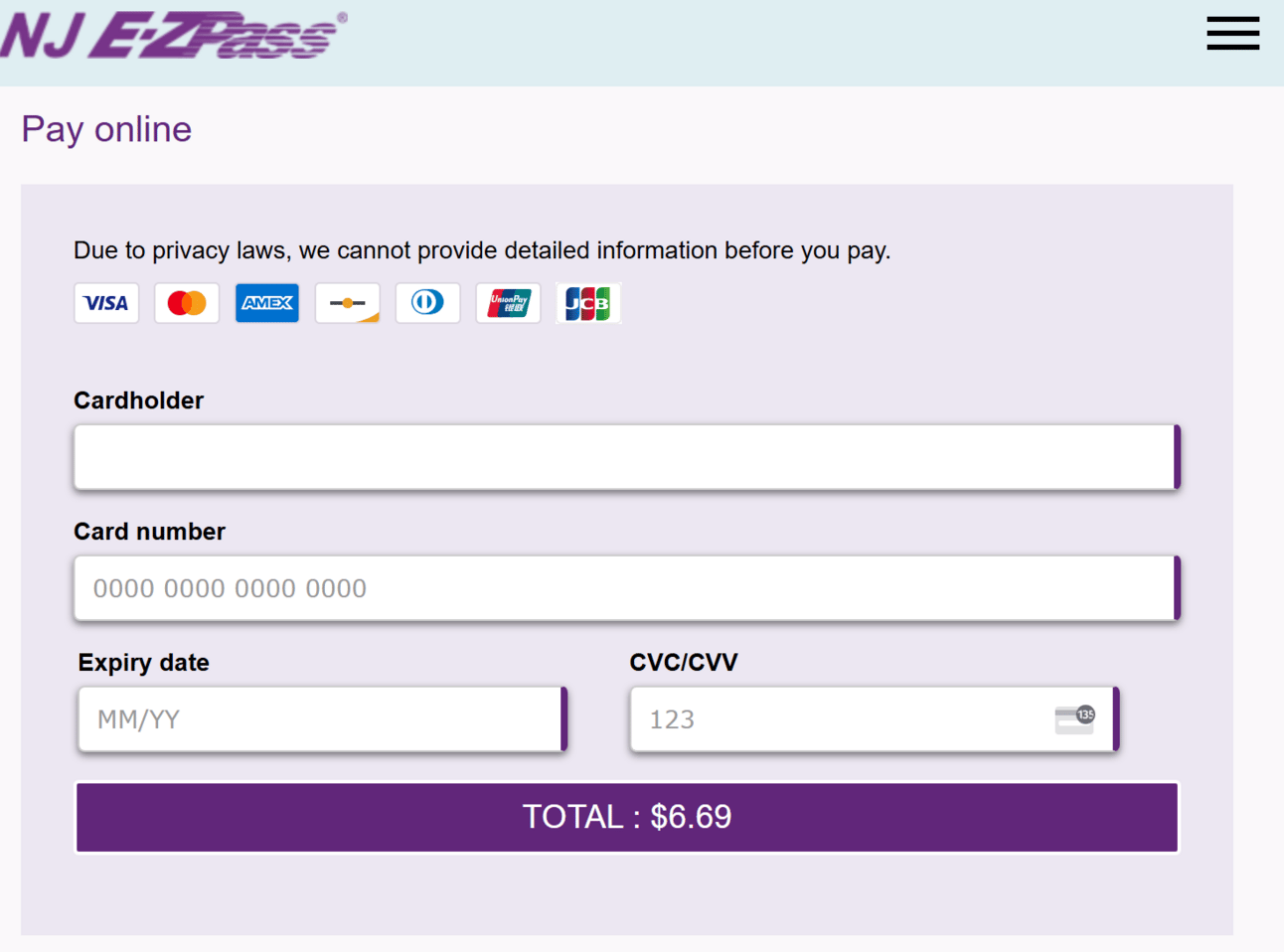
From there, I was directed to fill in my personal information because privacy laws prevented me from getting “detailed information” before I paid…right…

Some fake information later, I got to a payment page where I could pay my $6.69 toll.
At this point, I got greedy and played around with fake credit card information. After too many attempts, the site caught onto my shenanigans and started redirecting me to the blocked Google page. Alas, my new group thread abandoned me once more.
The scam is basic but effective. Similar scams tried to charge a $35 late fee. This one may have led to that after the initial $6 charge. But even if it didn’t, the small dollar amounts are enough that many people would just pay it without thinking about it.
Security & AI News
What Else is Happening?
🙃 They say impersonation is the greatest form of flattery, but the Computer Emergency Response Team of Ukraine (CERT-UA) disagrees. Attackers are calling up target victims and impersonating CERT-UA to trick users into allowing remote access to their systems. They ask the victim to install and accept a connection request over the AnyDesk remote access software. When it comes to the Internet, it’s best to remember…stranger danger.
💻 You remember Hewlett-Packard Enterprise (HPE), right? You may have bought their laptops a long time ago. And, now they…um, they do…um…well, I don’t know what they do anymore, but that didn’t stop a hacker known as “IntelBroker” from claiming to have stolen their data. IntelBroker claims the data includes source code and access keys to various HPE services. An investigation into what happened is ongoing.
↔ Chinese nation-state threat actors did the ol’ switcheroo in a new supply chain attack. The attackers compromised IPany, a South Korean VPN provider, and swapped the legitimate VPN installer with one that also installed a backdoor and malicious tools.
🤝 Iran and Russia inked a new deal to deepen the countries’ military, security, and technological ties. In a machine-translated version of the agreement, it calls out sharing “the intelligence and security services,” which would likely include cyber capabilities. Will anything come from this? Not sure. But the possibility of coordinating cyber attacks or disruption isn’t off the table.
😢 The new administration killed the Cyber Safety Review Board just before its third birthday. The CSRB was focused on reviewing significant cyber incidents and driving recommendations to drive improvements in the public and private sectors. They’re behind Microsoft’s scolding last year for not taking security seriously. I was a fan of the CSRB’s mission because it gave transparency into attacks that helped everyone learn. It also pushed Microsoft to publicly commit to more security.
If you enjoyed this, forward it to a fellow cyber nerd.
If you’re that fellow cyber nerd, subscribe here.
See you next week, nerd!

