I spent the start of the long weekend in the ER. What started as concerns over a blood clot just came down to overtraining, resulting in a ruptured cyst in my knee. How fun.
As for the dude next to me who was touting Ruby Tuesdays as an actual restaurant with high-quality food. No.
Anywho, today in the cyber world, we’re covering:
The White House cares about investing in cyber security, especially AI.
A new phishing kit with MFA bypass appears.
Protect yourself against scammers during tax season.
-Jason
AI Spotlight
They Really Do Care 😊

This week, the White House issued an executive order to strengthen and promote cybersecurity innovation, which made everyone in the cybersecurity community blush. It always feels nice when important people listen to you.
The executive order is long and covers nine major issues, but given this is the AI section, I will let you guess which topic we will deep-dive into. Good job! It’s the section titled Promoting Security with and in Artificial Intelligence.
The White House rightly noted that AI “has the potential to transform cyber defense by rapidly identifying new vulnerabilities, increasing the scale of threat detection techniques, and automating cyber defense.”
So what is the White House proposing we do about that? Well, here are the major actions that they are mandating happen:
Launch a program to use AI to enhance cyber defenses of critical infrastructure in the energy sector. This is broad, but they call out specific examples of what this could include, like vulnerability detection and automatic patch management. Patching quickly is a win.
Launch a program to use advanced AI models for cyber defense. This is also a bit vague, but I’m bullish about it for cybersecurity. We saw what AI did when it was infused in AV (hello, EDR), so expanding that capability will be a net positive.
Prioritize funding to create large-scale labeled datasets. These datasets will be fuel for training AI models. Even cooler is that they will open those to the broader academic research community, which will help fuel innovation.
Prioritize research in key areas. These include:
Human-AI interaction methods to assist defensive cyber analysis
Security of AI coding assistance, including the security of AI-generated code
Methods for designing secure AI systems
Methods for prevention, response, remediation, and recovery of cyber incidents involving AI systems.
A focus on understanding AI software vulnerabilities and compromises. This makes sense, given we are walking into a whole new world of security vulnerabilities and incidents that are strictly the result of AI. It’s best not to get caught flat-footed there.
Now, this is the government we’re discussing, so let’s not expect anything groundbreaking in the next few months. The important thing here is that it narrows the focus of initiatives for key government agencies. When you can narrow the focus, drive collaboration between public and private institutions, and have funding allocated behind all of that, there is a greater opportunity for good things to happen.
Security Deep Dive
A New Fancy Phishing Kit
We can’t go on a nice walk without running into a new attack tool kit. This time, a new wild Adversary-in-the-Middle (AiTM) phishing kit appeared that is targeting M365 accounts. It goes by “Sneaky 2FA.” Researchers at Sekoia, dropped the deets in a recent blog post.
Cybercriminals interested in purchasing access to the phishing kit must first interact with Sneaky Log, a fully featured Telegram bot.
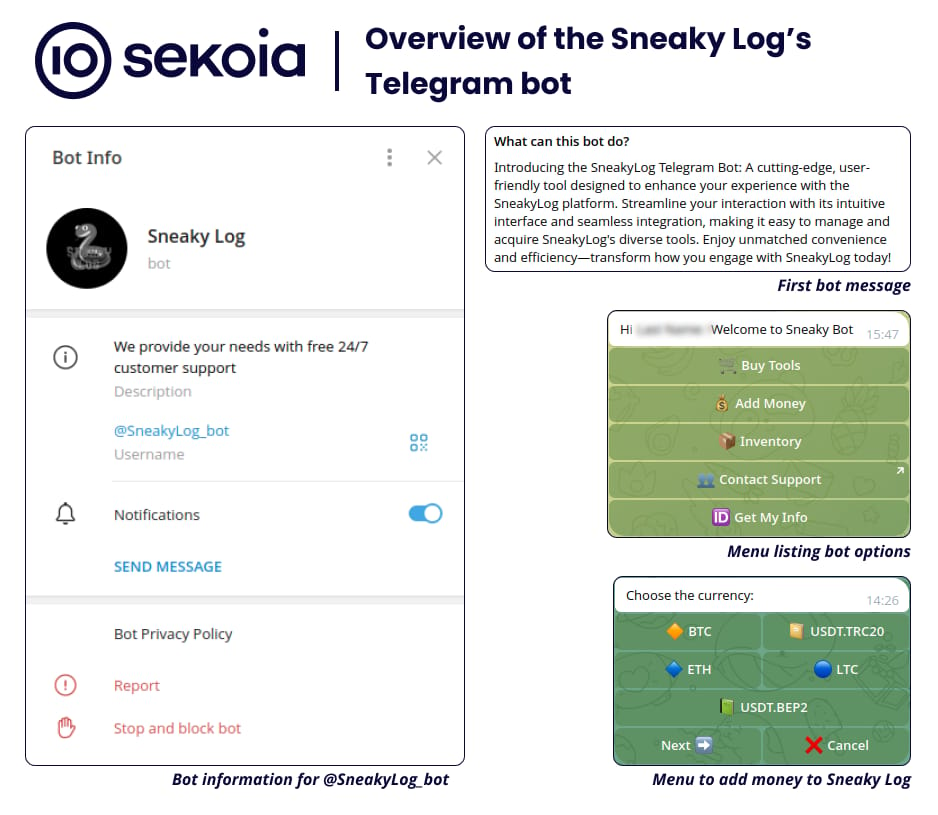
Cybercriminals who purchase it using one of five digital assets (shown above) are given a licensed version of the source code and must deploy it themselves…not much of a full-service Phishing-as-a-Service (PhaaS) solution if you ask me.
Here are some of the cool features that Sneaky 2FA provides that make it extra sneaky:
Traffic Filtering: The phishing page will check where the victim’s IP address originates from. If it comes from a place that doesn’t jive with a user (like an Internet Service Provider), it redirects the user to a Microsoft-related Wikipedia page.
Cloudflare turnstile: The phishing page will check to make sure the visitor is human. This is an easy way to filter out security checks and adds a bit of legitimacy. I see this popping up more and more now.
Email Autofill: The fake M365 login page automatically fills in the victim’s email address. While this sounds basic, it reduces friction for the user.
MFA Bypass: The fake M365 login page prompts the user for their MFA of choice, which can be an authenticator app or SMS. I have a video explaining how this works on the backend.
These types of phishing kits are the future of phishing. With MFA bypass built into phishing kits, there needs to be a stronger push to switch to a phishing-resistant MFA solution cough passkeys cough.
Security & AI News
What Else is Happening?
💰 You may hate tax season, but scammers love it. Scammers try to submit tax returns on your behalf. Not out of kindness. They only want to get that tax refund before you do. The IRS recommends setting up an IP PIN, which you can create here.
🪣 Ransomware actors are targeting AWS S3 buckets. If you’re unfamiliar with S3 buckets, they are just digital buckets where you can store your data. Attackers first find leaked or stolen AWS keys and then encrypt your files using AWS built-in encryption tools. To add salt to the wound, they then mark files for deletion after seven days to add pressure to pay.
🧽 The FBI remotely removed PlugX malware from over 4,200 devices that were infected in the US. They did this by using the malware’s own “self-delete” functionality against it. I’m a big fan of law enforcement efforts to dismantle botnets by cleaning up infected systems when possible. There’s another camp that prefers law enforcement to stay out of their way and would rather live with an infected system that sends all of their data to a threat actor. But, hey, to each their own, I guess.
🤣 Attackers are trying to compromise Google Ads accounts by tricking users with Google Ads. Classic. The attackers create a Google Ad that impersonates the Google Ads login page. Victims trying to log into their Google Ads account may search Google for the login page. The attacker’s ad that mimics the login page shows up, which the victim then clicks. When they enter their credentials on the phishing page, they go straight to the attacker.
🪆 Researchers at Ukraine’s State Service for Special Communications and Information Protection (oof, I need to take a breath after that one) summarized Russia’s cyber attacks against Ukraine last year. The attacks focused on espionage, financial theft, and psychological damage, and the majority of them were traced back to three Russia-linked hacker groups.
If you enjoyed this, forward it to a fellow cyber nerd.
If you’re that fellow cyber nerd, subscribe here.
See you next week, nerd!

